The Reality of AI Security Has Changed.
StrikeVault, Your Security Will Never Be the Same.
The Principle Behind StrikeVault.
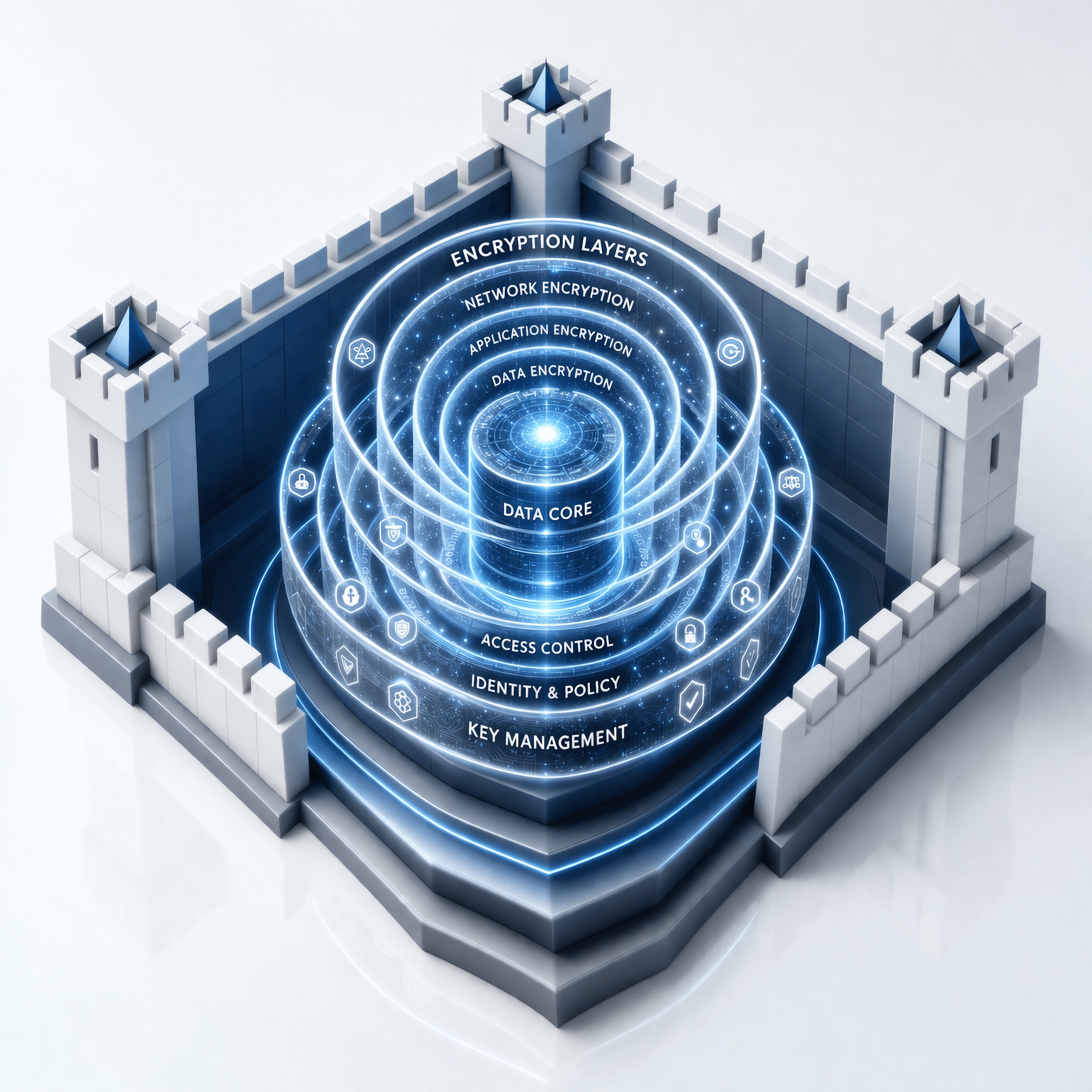
Instead of: protecting systems, enforcing policy at the perimeter, trusting infrastructure.
Protect the DATA itself.
Embed policy into the data.
Rely on mathematics.
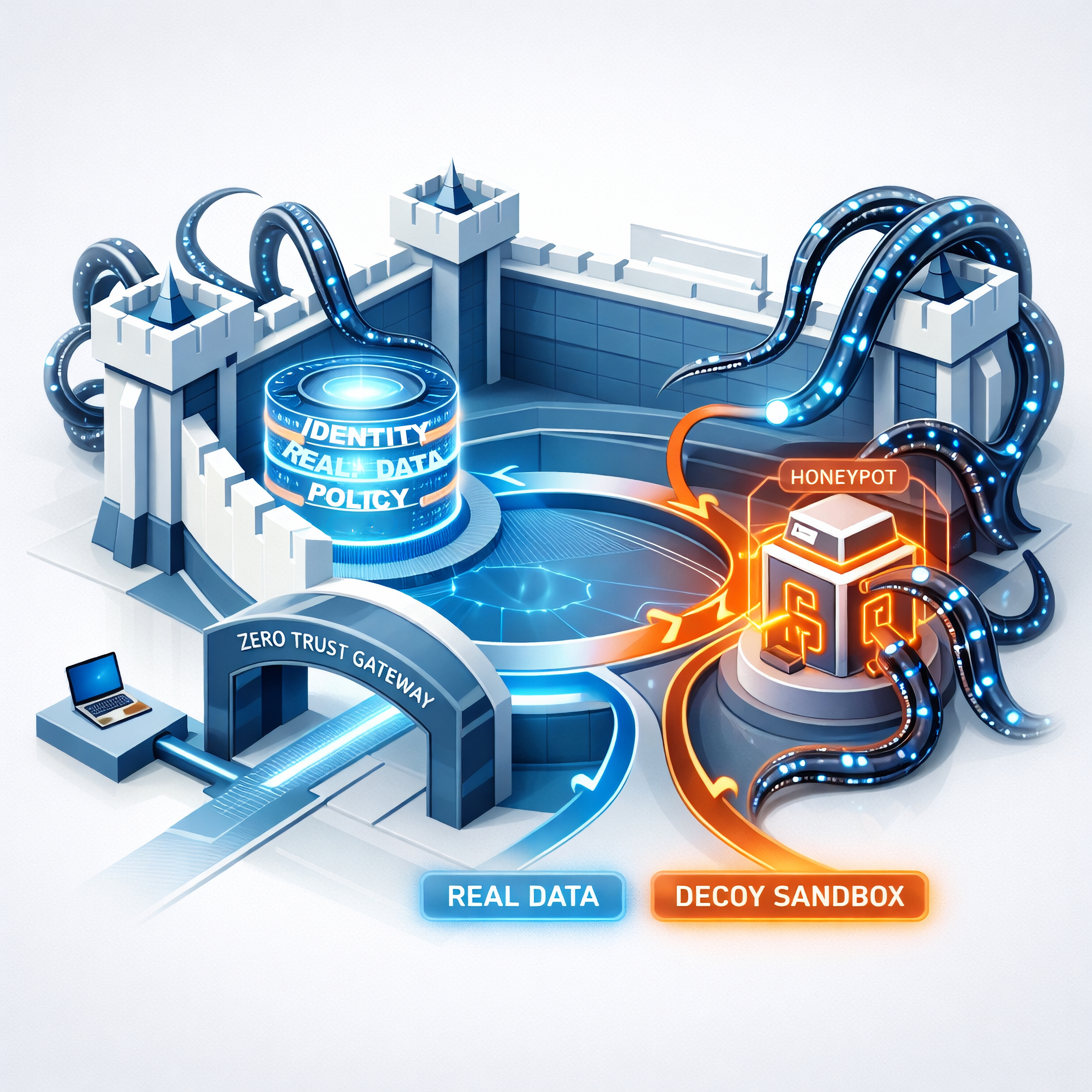
This is what we call: The Physics of Zero Trust

How StrikeVault Works
Every piece of data becomes a Self-Enforcing object.
It carries its own policy generation.
It validates identity locally.
It determines whether it can be opened.
It logs every interaction.
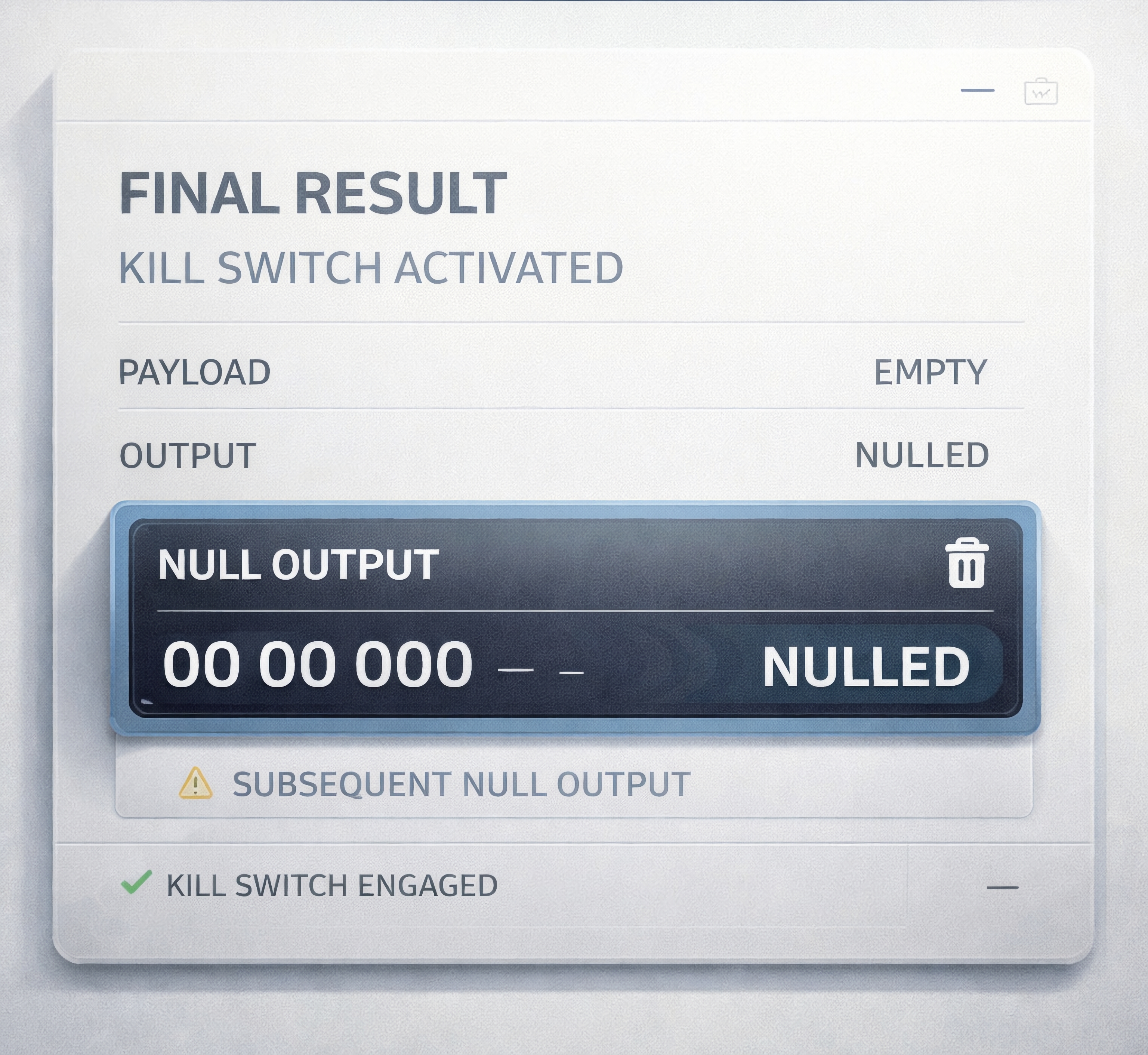
IF the conditions are not met:
The data does not open.
It's not denied.
It's not flagged.
IT is now, mathematically inaccessible.
Protect from Breach, Loss, and Disruption.
Made and tested for the United States Navy SBIR progam.
Revenue Protection
IP Protection
Peace of Mind
CLICK BELOW TO WATCH FIRST!
Built for Military standards
Is StrikeVault for you?
Federal AGencies
Enterprise companies
State Government
Commercial Companies
local government
small business
Today's reality is in a constant state of change.
Every system we operate today was built on a simple assumption: Control the Network, then we control the data.
That Assumption, has changed. AI systems operate differently and so should our controls
AI systems require data to be exposed, in memory, in prompts, in inference pipelines.
And when DATA is Exposed, Control is LOST
There are two organizations today. The first are keeping their heads down and waiting for the AI bubble to go away.
The second understands these systems operate differently, they want to avoid failure, and are proactive.
WHAT TYPE OF ORGANIZATION ARE YOU?
What is Actually Happening?
DATA is no longer at rest or in transit, it's in use.
Most security tools have no authority here.
Identity has become portable, fragile, breachable.
A single, compromised token can act as a master key.
AI systems can't distinguish between, Trusted or Malicious inputs.
Our prompts, have become the attack surface.
THIS IS NOT A TOOLING PROBLEM. IT IS A DESIGN PROBLEM.
GDPR
Compliant
HIPAA
Compliant
NIST
Compliant
FOLLOW US
COMPANY
CUSTOMER CARE
LEGAL
Copyright . . All Rights Reserved.